Recommended Azure Cost Estimate
Only the recommended environment is priced here. This is the proposed client budget line for a secure, production-shaped test estate in Azure.
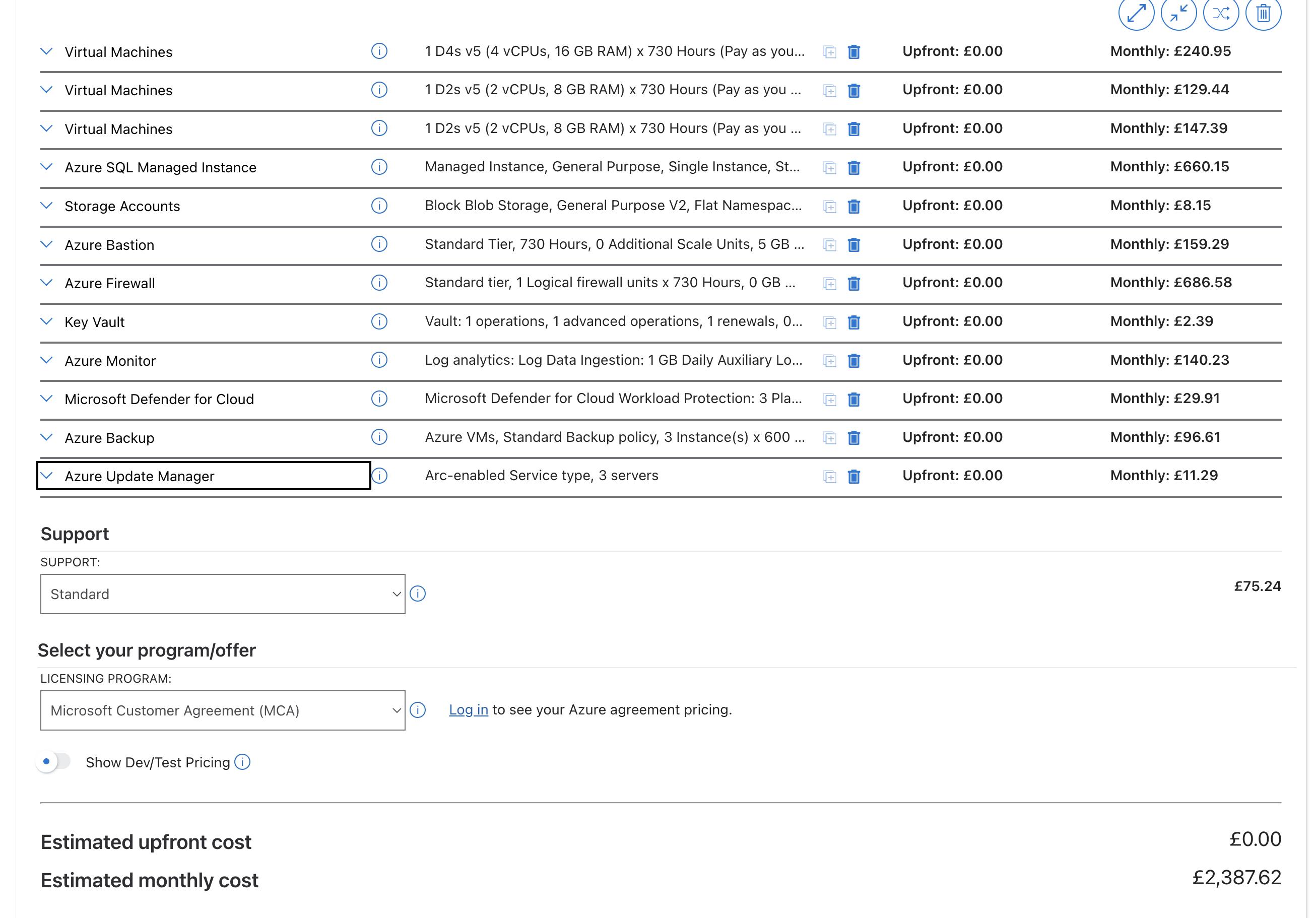
Calculator-backed estimate from the Azure pricing export for UK South, Pay-As-You-Go, dated 16 April 2026. This is the current planning figure for the recommended environment.
Why The Estimate Looks Higher Than A Simple Lab
- The design is isolated by intention — the firewall, Bastion, and private SQL path are there to stop any accidental production contact.
- The environment is supportable — backup, monitoring, patching, and security scanning are included rather than left as hidden follow-on work.
- The layout mirrors reality — separate web, worker, and build / restore roles produce more trustworthy test results than a single combined server.
- The database tier is compatible — SQL Managed Instance is used because Pearl relies on SQL features that simpler options would not reproduce safely.
Monthly Baseline
The current calculator export total for the recommended build.
RecommendedAnnual View
Use this for annual approval and client budgeting conversations.
Largest Cost Drivers
Firewall, SQL Managed Instance, and the 3 VMs together make up most of the total.
Pricing Calculator Reference
This estimate was taken from the official Microsoft Azure Pricing Calculator. The screenshot below is included as the visual source reference used for this client-ready summary. Source: azure.microsoft.com/en-us/pricing/calculator/
| Azure Service | Recommended Baseline | Monthly Cost | Purpose in Plain English | Why It Is Recommended |
|---|---|---|---|---|
| VM1 — Web Tier | D4s v5, 4 vCPU, 16 GB RAM, 128 GB P10 OS disk, 256 GB P15 data disk | £240.95 | Runs the websites, internal web services, search, and cache. This is the customer-facing side of the estate. |
It needs the strongest VM size because it hosts the broadest mix of workloads and is the best place to preserve realistic front-end behaviour. |
| VM2 — Worker Tier | D2s v5, 2 vCPU, 8 GB RAM, 128 GB P10 OS disk | £129.44 | Runs background processing such as queue jobs, health checks, AI spooler activity, and Totem. |
Separating worker activity from the web tier makes test behaviour cleaner and much closer to the live platform. |
| VM3 — Build / Restore Tier | D2s v5, 2 vCPU, 8 GB RAM, 128 GB P10 OS disk, 128 GB P10 data disk | £147.39 | Handles CI/CD, deployment jobs, backup downloads, restores, and masking automation. |
It keeps engineering and restore work away from the servers used for active testing, which reduces interference and makes support easier. |
| Azure SQL Managed Instance | General Purpose, 4 vCores, 256 GB storage | £660.15 | Stores the full restored Pearl database set and supports the SQL behaviour the platform expects. |
Managed Instance is the compatibility-safe choice, while General Purpose avoids paying for production-grade high availability that test does not need. |
| Azure Blob Storage | General Purpose v2, Hot, LRS, 500 GB | £8.15 | Stores backup files, restore artefacts, and related automation content. |
It is the lowest-cost way to support the weekly refresh process and hold multiple backup copies ready for use. |
| Azure Bastion | Standard SKU | £159.29 | Provides secure admin access to the servers without public RDP exposure. |
Recommended because it reduces internet exposure and gives a much stronger security story to the client. |
| Azure Firewall | Standard SKU | £686.58 | Acts as the outbound gatekeeper for the environment so only approved destinations can be reached. |
This is the control that stops the test estate from accidentally touching live integrations or production-only services. |
| Azure Key Vault | Standard tier | £2.39 | Keeps secrets like passwords, connection strings, and API keys in a secure central vault. |
Recommended because it prevents secrets from spreading into server files, scripts, and manual notes. |
| Azure Monitor + Log Analytics | Workspace, diagnostics, alerting, application insights | £140.23 | Collects logs, metrics, and alerts in one place so issues can be diagnosed quickly. |
Recommended because a complex environment without central monitoring becomes expensive and slow to support. |
| Microsoft Defender for Cloud | 3 protected servers, SQL, storage, Key Vault | £29.91 | Checks the environment for vulnerabilities, missing controls, and suspicious security signals. |
Recommended so the test estate does not become the easiest point of compromise in the wider platform. |
| Azure Backup | 3 protected VMs, LRS backup storage | £96.61 | Provides restore points for the VMs if a release, experiment, or admin mistake breaks the servers. |
Recommended because fast rollback is far cheaper than rebuilding multiple Windows servers by hand. |
| Azure Update Manager | 3 managed servers | £11.29 | Automates patching and helps keep the test servers current and supportable. |
Recommended because test estates are often where patching discipline slips first, creating avoidable risk. |
| Microsoft Support Plan | Azure support coverage | £75.24 | Provides a formal escalation route to Microsoft for Azure platform issues. |
Recommended because issues involving SQL Managed Instance or Azure networking sometimes need vendor-level support. |
| Total Recommended Monthly Cost | Recommended test environment baseline | £2,387.62 | Annual view: £28,651.44. This is the current calculator-backed planning total for the recommended estate. |
|
Where The Spend Sits
The bulk of the spend is in the controls that make the environment usable and safe: secure networking, SQL compatibility, and the three-server role split.
Conclusion
The recommended Azure budget is justified because it buys safe change capability. It gives MessageDirect a realistic place to test releases, restore masked data, validate integrations, and troubleshoot issues without putting the live 24/7 Pearl service at risk.
In practical terms, this is the cost of moving from production-first testing to a controlled engineering platform. That is why the recommendation is to fund this build as proposed rather than strip out the controls that make it credible.