Recommended Azure Cost Estimate
This is the client-ready cost estimate for the recommended build only: the approved 3-VM split, one Azure SQL Managed Instance, and the supporting Azure services needed to keep the environment secure, recoverable, and properly isolated from production.
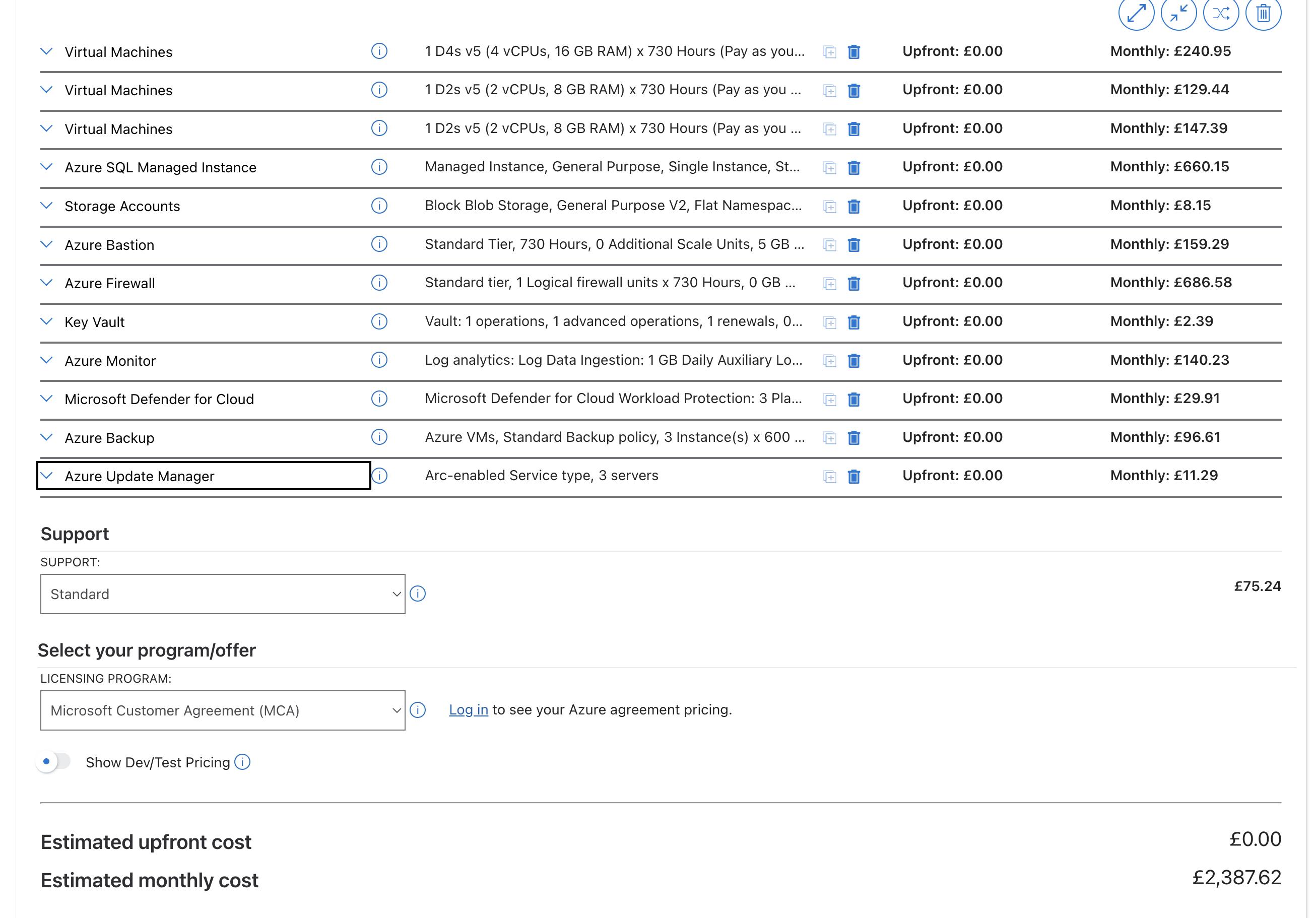
Based on the exported Microsoft Azure Pricing Calculator estimate in UK South, Pay-As-You-Go, dated 16 April 2026. This is the current safe planning baseline for the recommended environment.
What This Budget Actually Buys
- A production-shaped test platform with separate web, worker, and build / restore roles instead of one overloaded all-in-one server.
- Safe administration through Bastion and a private-only SQL path, so the environment is not exposed directly to the internet.
- Controlled outbound traffic through Azure Firewall, which stops the test environment from accidentally touching live payment, SMS, telephony, or email systems.
- Operational resilience through backup, monitoring, patching, and security scanning so the team can test confidently without creating a support burden.
Monthly Baseline
Current calculator export total for the full recommended environment.
Recommended budget lineAnnual View
Useful for annual planning, internal approval, and client budget framing.
Main Cost Drivers
Firewall, SQL Managed Instance, and the 3 VMs together account for about 78% of the total.
Pricing Calculator Reference
This estimate was taken from the official Microsoft Azure Pricing Calculator. The screenshot below is included as the visual source reference used for the client-facing cost breakdown. Source: azure.microsoft.com/en-us/pricing/calculator/
| Azure Service | Recommended Baseline | Monthly Cost | Purpose in Plain English | Why This Is Recommended |
|---|---|---|---|---|
| VM1 — Web Tier | D4s v5, 4 vCPU, 16 GB RAM, 128 GB P10 OS disk, 256 GB P15 data disk | £240.95 | Runs the Pearl websites, internal web services, cache, and search. In simple terms, this is the front door that serves pages, handles requests, and keeps the user-facing side responsive. |
This is the one server that needs the most headroom because it carries IIS, Memcached, and Solr together. The chosen size is large enough for realistic testing without paying for a production-scale machine. |
| VM2 — Worker Tier | D2s v5, 2 vCPU, 8 GB RAM, 128 GB P10 OS disk | £129.44 | Runs the background jobs that users do not see directly, such as queue processing, health checks, AI spooler activity, and the Totem notification service. |
Keeping this work off the web server protects test fidelity and matches how the live platform behaves. The smaller VM is enough because these services are mostly waiting on I/O rather than using heavy CPU. |
| VM3 — Build / Restore Tier | D2s v5, 2 vCPU, 8 GB RAM, 128 GB P10 OS disk, 128 GB P10 data disk | £147.39 | Handles builds, deployments, backup downloads, database restores, and masking scripts. This is the engineering workbench for the environment. |
Builds and restore jobs can be noisy and storage-heavy. Giving them their own server avoids slowing down test activity on VM1 and VM2 and makes the environment easier to support. |
| Azure SQL Managed Instance | General Purpose, 4 vCores, 256 GB storage | £660.15 | Stores all 17 Pearl databases and provides the SQL features the application expects, including cross-database behaviour that simpler database services do not handle well. |
Managed Instance is the right fit because it behaves much more like the current SQL estate. General Purpose keeps compatibility while avoiding the higher Business Critical price that test does not need. |
| Azure Blob Storage | General Purpose v2, Hot, LRS, 500 GB | £8.15 | Acts as the landing zone for weekly backup files, restore artefacts, and a small amount of supporting automation content. |
It is the cheapest practical way to keep several weekly copies ready for refresh work. This is a low-cost, high-value part of the design. |
| Azure Bastion | Standard SKU | £159.29 | Provides secure browser-based admin access to the Windows servers without exposing remote desktop ports or public IPs on the VMs. |
This is recommended because it sharply reduces the attack surface and gives a cleaner, more defensible security story for the client. |
| Azure Firewall | Standard SKU | £686.58 | Works as the outbound checkpoint for the whole estate. It decides what the environment is allowed to contact outside Azure. |
This is what keeps the test environment truly isolated. It prevents accidental calls to live payment gateways, live SMS routes, live email flows, or production-only destinations. |
| Azure Key Vault | Standard tier | £2.39 | Stores passwords, connection strings, API keys, and certificates in one controlled vault instead of scattering secrets across servers and config files. |
It is recommended because it removes one of the most common causes of security drift: secrets copied into scripts, notes, or server folders. |
| Azure Monitor + Log Analytics | Workspace, diagnostics, alerting, application insights | £140.23 | Collects logs, metrics, alerts, and diagnostic events from the servers, SQL, firewall, and supporting Azure services. |
Without it, every issue becomes a manual investigation across multiple machines. With it, the team gets one place to troubleshoot and prove what happened. |
| Microsoft Defender for Cloud | 3 protected servers, SQL, storage, Key Vault | £29.91 | Continuously checks the environment for vulnerabilities, missing controls, and suspicious security events. |
Recommended because a weaker test environment can become the easiest route into the wider estate. This keeps the security posture close to production. |
| Azure Backup | 3 protected VMs, LRS backup storage | £96.61 | Creates recoverable restore points for the servers so the team can roll back quickly if a deployment or test change breaks the environment. |
Recommended because rebuilding multiple Windows servers manually is slow and expensive. Backup reduces recovery time and lowers operational risk. |
| Azure Update Manager | 3 managed servers | £11.29 | Automates Windows patching so the environment stays current without someone having to maintain each server by hand. |
Recommended because patching is often skipped on test platforms first. This keeps the estate supportable and avoids preventable security issues. |
| Microsoft Support Plan | Azure support coverage | £75.24 | Gives access to Microsoft support engineers if there is a platform problem with Azure networking, SQL Managed Instance, or service-level issues. |
Recommended because some Azure issues cannot be solved from inside the project team alone. It shortens outage time and gives a formal escalation path. |
| Total Recommended Monthly Cost | Recommended test environment baseline | £2,387.62 | Annual view: £28,651.44. This is the current calculator-backed baseline for the proposed test estate. |
|
Where The Spend Sits
The biggest cost items are the firewall, the database tier, and the three servers themselves. That is expected: isolation, SQL compatibility, and role separation are the three design choices that make this environment useful rather than just cheap.
Important Planning Notes
This estimate is the current calculator export, not a discounted contract rate. It is suitable for planning and client presentation, but not a commercial quote.
The VM lines in the export were costed at full monthly runtime. Once business-hours auto-shutdown is applied, day-to-day compute spend should land lower than this baseline.
SQL Managed Instance stays on all the time. That is why its cost remains one of the dominant line items even if the VMs are scheduled down overnight.
Potential optimisations exist later. Azure Hybrid Benefit or reserved pricing could reduce costs once the client commits to the estate long term, but those savings should not be assumed up front.
Conclusion
The recommended test environment is worth funding because it removes live operational risk, not because it is the cheapest possible build. At about £2.39k per month, MessageDirect gets a secure, production-shaped platform where releases, restores, integration changes, and troubleshooting can happen safely before anything reaches the live Pearl service.
The cost is driven by the controls that make the environment credible: proper SQL compatibility, secure private access, outbound isolation, and recoverability. Those are exactly the controls the client is buying, and they are what turn this from a simple lab into a safe engineering platform.